Some ideas are timeless. Back in 2004, an anonymous genius set up "FobCam". Tired of having to carry around an RSA SecurID token everywhere, our hero simply left the fob at home with an early webcam pointing at it. And then left the page open for all to see. Security expert Bruce Schneier approved of this trade-off between security and usability - saying what we're all thinking: Here’s a guy w…
Continue reading →
There's a new Web Standard in town! Meet WebMonetization - it aims to be a low effort way to help users passively pay website owners. The pitch is simple. A website owner places a single new line in their HTML's <head> - something like this: <link rel="monetization" href="https://wallet.example.com/edent" /> That address is a "Payment Pointer". As a user browses the web, their browser takes …
Continue reading →
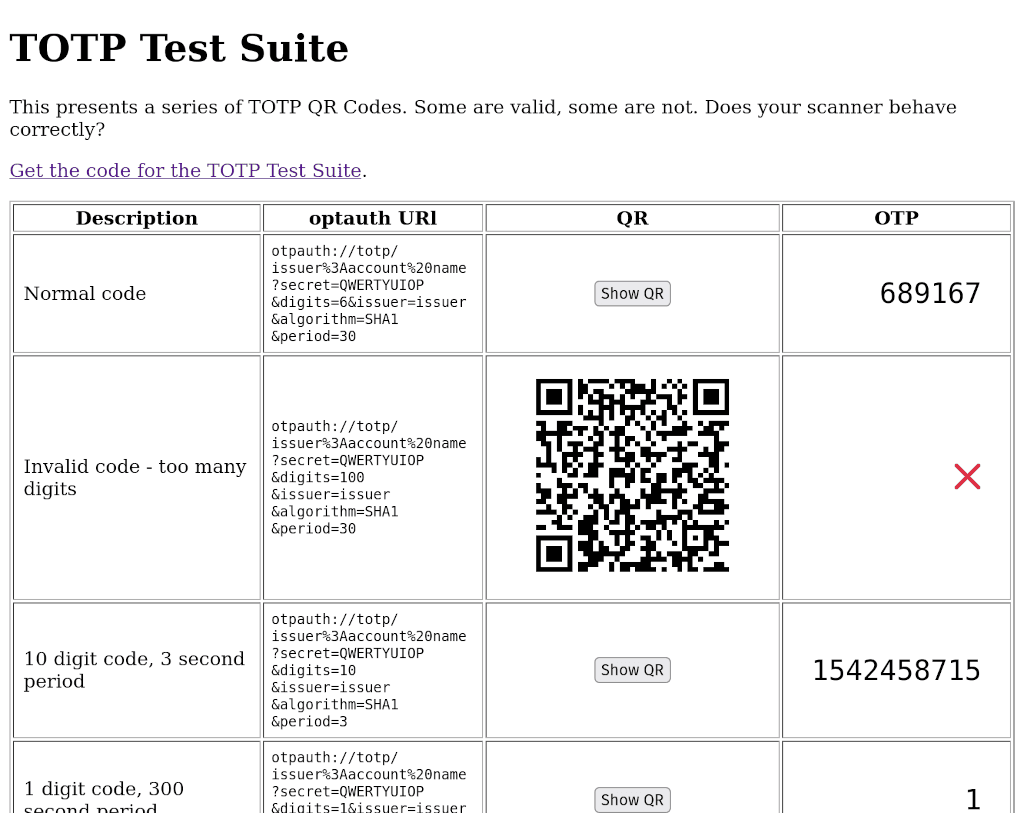
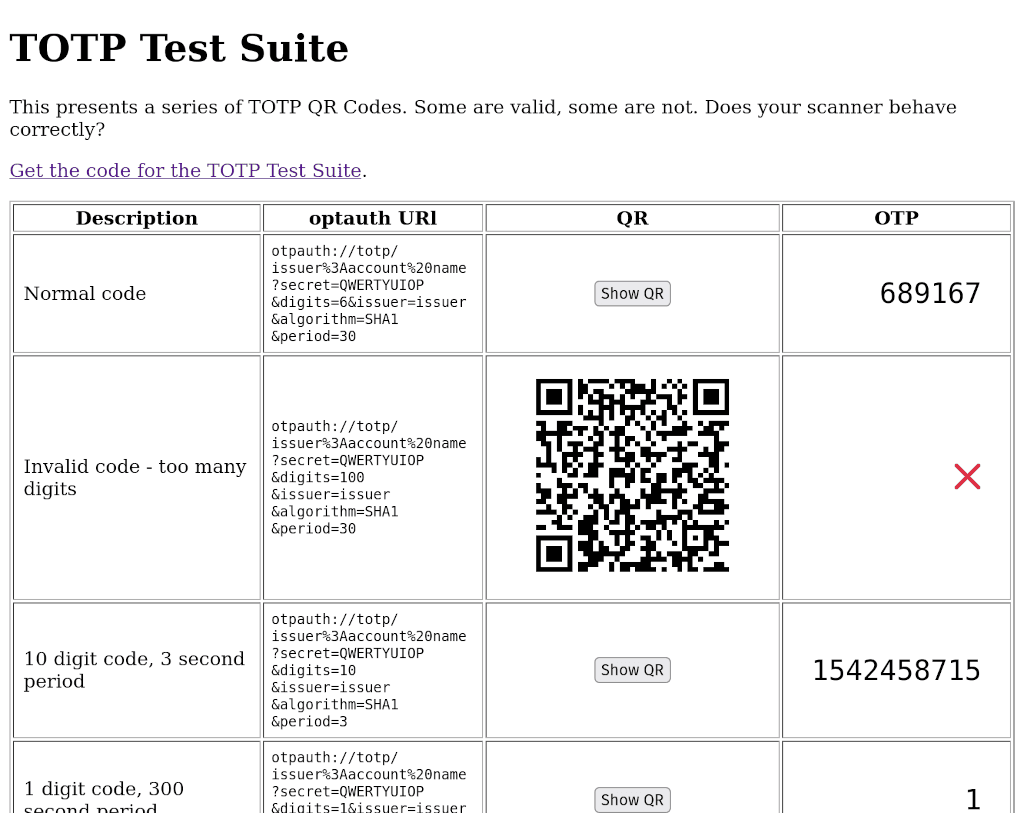
Because I'm a massive nerd, I actually try to read specification documents. As I've ranted ad nauseam before, the current TOTP spec is irresponsibly obsolete. The three major implementations of the spec - Google, Apple, and Yubico - all subtly disagree on how it should be implemented. Every other MFA app has their own idiosyncratic variants. The official RFC is infuriatingly vague. That's no…
Continue reading →

The Web Crypto API is, thankfully, nothing to do with scammy cryptocurrencies. Instead, it provides access to powerful cryptographic features which were previously only available in 3rd party tools. So, is it possible to build a TOTP code generator without using any external JS libraries? Yes! And it is (relatively) simple. Here's the code that I've written. It is slightly verbose and contains…
Continue reading →

If you use Multi-Factor Authentication, you'll be well used to scanning in QR codes which allow you to share a secret code with a website. These are known as Time-based One Time Passwords (TOTP). As I've moaned about before, TOTP has never been properly standardised. It's a mish-mash of half-finished proposals with no active development, no test suite, and no-one looking after it. Which is…
Continue reading →

Android is belatedly getting a Bluetooth tracker feature which doesn't rely on proprietary apps. Long-time readers will know that back in 2016 I reviewed both the Chipolo and the TinTag. Both of those were adequate at finding things which were in range of your phone, but hopeless at finding lost items - because they required everyone to have a special app installed. But now, under pressure from …
Continue reading →
Here's a "fun" thought experiment. Imagine a website which let you sign in using only your username and TOTP code. No passwords. No magic links emailed to you. No FIDO tokens. No codes via SMS. Just a TOTP generated and displayed on your device. Is that useful? Sensible? Practical? It's certainly technically possible. Store the username, store the TOTP seed, done. Your users can now log in. …
Continue reading →

A decade ago, I appeared on the 361 Podcast to give my advice about mobile security. This was the era of the iPhone 5 and Android KitKat. BlackBerry was trying to have (yet another) resurgence and Nokia was desperately trying to keep Windows Phone alive. What advice did I give then, and is it still relevant? Stay Sceptical In at number five is just stay sceptical. I mean, quite often, lots…
Continue reading →

For lots of online accounts, a date of birth is nothing more than a very weak second factor. The majority of places aren't checking your identity, cross-referencing your birthdate, and personalising your experience based on your Zodiac sign. At most, they'll wish you a happy birthday and / or let you recover your account by providing your date of birth. But, of course, lots of people know your…
Continue reading →
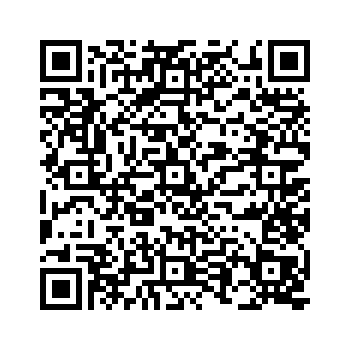
Yeah. Yeah, I reckon so. Under the right circumstances. Multi-Factor Authentication (MFA, 2FA, TOTP, whatever you want to call it) is pretty nifty. You scan a QR code and your phone will continually generate a set of one-time passwords which are synchronised with a remote server. There's nothing stopping multiple people from scanning that QR code! They will each have the same password displayed …
Continue reading →

I've been writing about QR codes since 2007 - long before they were fashionable. Because QR Codes are so cheap to produce, there has always been a concern that attackers might print out their own codes and stick them over legitimate ones. When I first wrote about QR Hijacking in 2011, I said that such attacks were usually easy to spot: Recently, a new wave of QR Hijacking attacks have been…
Continue reading →

Shakespeare, famously, shunned computers. Like some sort of retro hipster, he didn't write his plays on a laptop, refused to use spellcheck, and didn't register his copyright on the blockchain. Lord, what fools these mortals be! What would Shakespeare's plays have been like if their characters understood basic cybersecurity? Now, it is true that very few of his plays feature computers, but…
Continue reading →