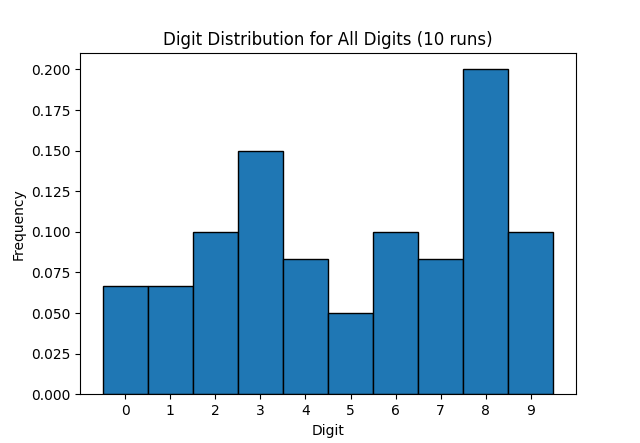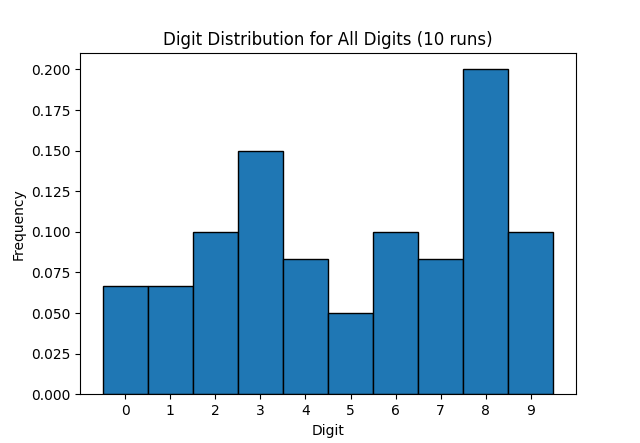
I'm pretty sure that the 2FA codes generated by my bank's TOTP app have a bias towards the number 8 - because eight is an auspicious number. But is that just my stupid meaty brain noticing patterns where none exist? The TOTP algorithm uses HMAC, which in turn uses SHA-1. My aforementioned brain is not clever enough to understand how that works. Although bigger, meatier brains have assured me it …
Continue reading →

Recently, WordPress got in contact with me to say they suspect that my password was exposed in some sort of data breach. Well, it's a day ending with a "y" - so of course some scumbag has pilfered my digital identity. WordPress mandated that I change my password. But was that really necessary? Firstly, the password was uniquely generated by my password manager. It isn't re-used anywhere else.…
Continue reading →
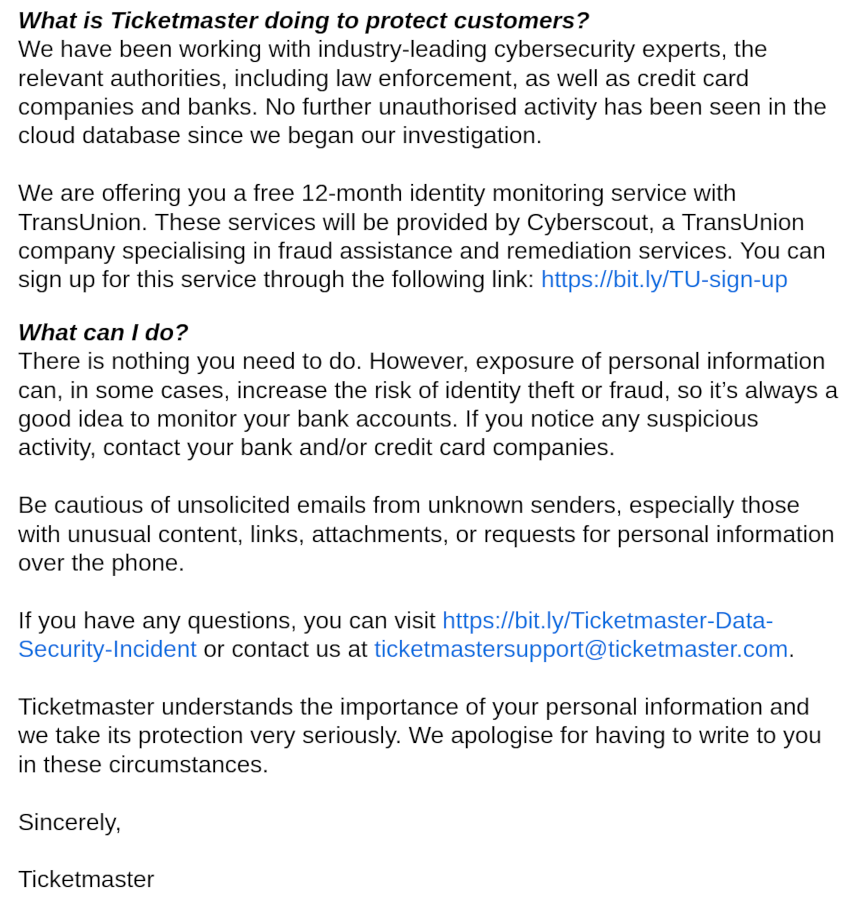
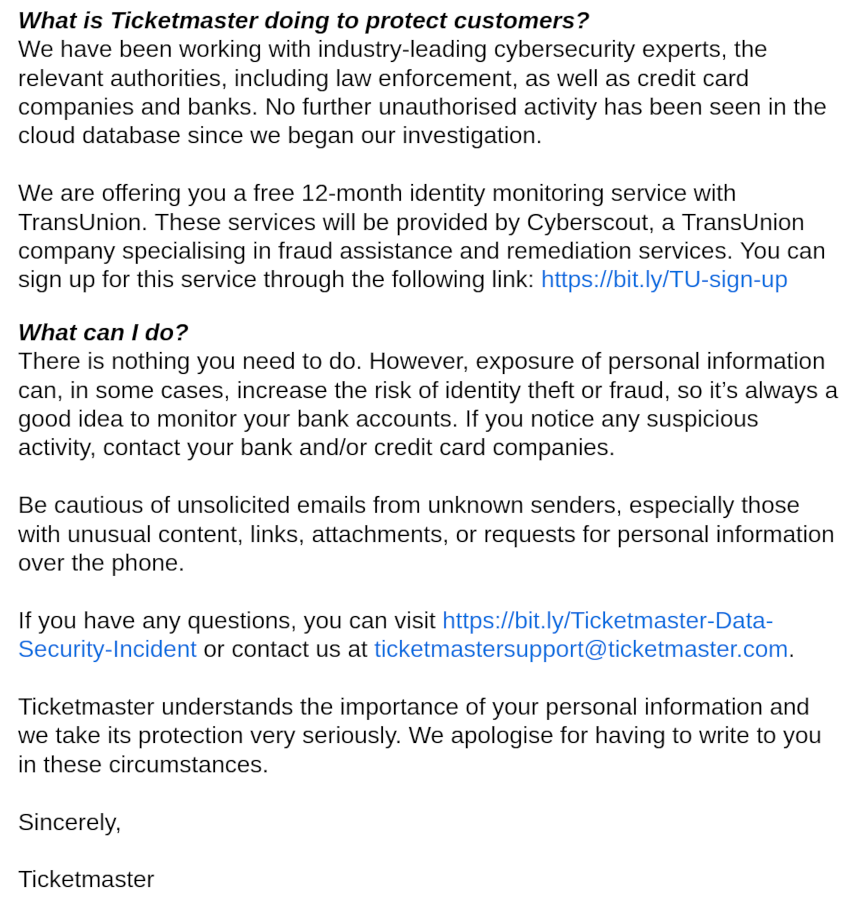
TicketMaster has joined the long list of companies to lose their customers' information. As is common, they sent out an email to warn poor sods like me who might have had our details snaffled. Their email is particularly poor and contains a delightful example of how not to communicate issues like this. See if you can spot it: In the same breath as warning their customers to look out for…
Continue reading →

Over the last few weeks, I've had several people ask me about the recent hack on the NHS. A ransomware attack has meant that several hospitals have cancelled operations and there is now an urgent demand for blood donors. What does it say about the state of NHS IT that this attack has happened? Nothing. Because the NHS was not hacked. Instead, a company they use to perform blood tests was…
Continue reading →

Everyone loves Dark Mode. It is kinder on the eyes, less energy intensive, and looks hecking cool. *5 seconds later* We regret to inform you that Dark Mode causes security bugs. (With apologies to Ben Ward) OK, OK. This isn't a particularly severe security bug, but I found it interesting. The Matrix messaging app "Element" lets you sign in to your account on multiple devices. In order to…
Continue reading →

You receive a call on your phone. The polite call centre worker on the line asks for you by name, and gives the name of your bank. They say they're calling from your bank's fraud department. "Yeah, right!" You think. Obvious scam, isn't it? You tell the caller to do unmentionable things to a goat. They sigh. "I can assure you I'm calling from Chase bank. I understand you're sceptical. I'll…
Continue reading →

It is tempting to think that users are to blame for their own misfortune. If only they'd had a stronger password! If only they didn't re-use credentials! If only they had perfect OpSec! If only...! Yes, users should probably take better care of their digital credentials and bury them in a digital vault. But there are some things which are simply impossible for a user to protect against. Take,…
Continue reading →
It's never great to find out you're wrong, but that's how learning and personal growth happens. HTTP Message Signatures are hard. There are lots of complex parts and getting any aspect wrong means certain death. In a previous post, I wrote A simple(ish) guide to verifying HTTP Message Signatures in PHP. It turns out that it was too simple. And far too trusting. An HTTP Message Signature is a…
Continue reading →
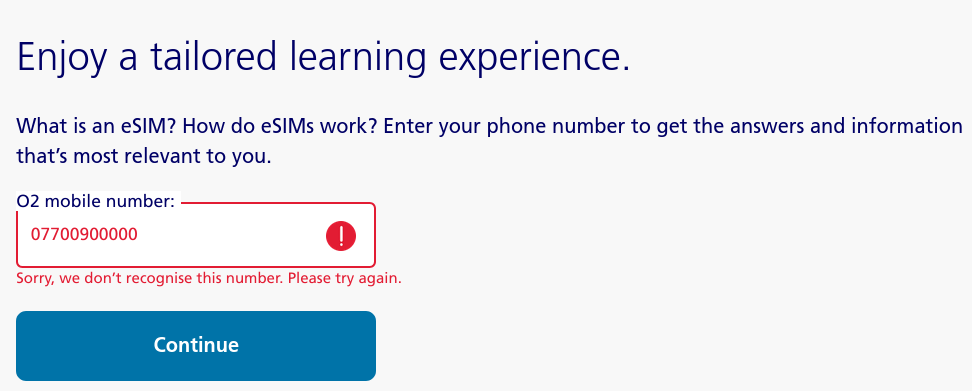
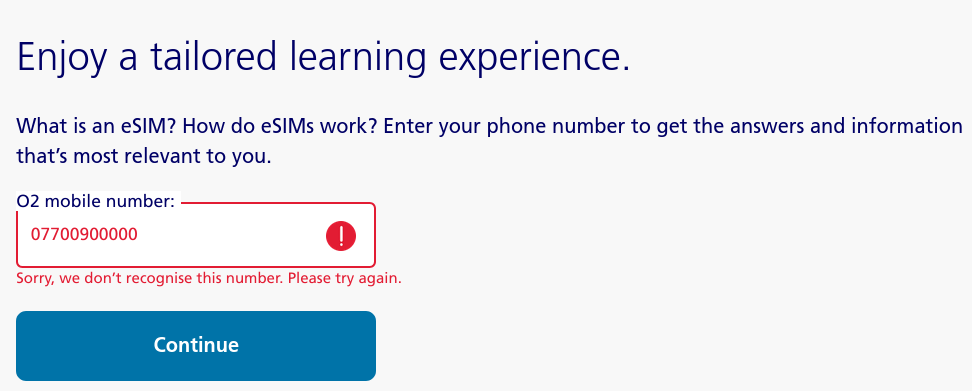
It's always fun keeping your network inspector tab open. While looking around the O2 UK website, I found this page all about eSIMs. For some reason, it wants to know the user's phone number. I put in a random number, and it refused to let me in. Putting in a genuine O2 number let me through. So what is it doing to validate numbers? It is making an API call to this URl: …
Continue reading →

I'm trying to get my head round HTTP Signatures as they're used extensively in the Fediverse. Conceptually, they're relatively straightforward. You send me a normal HTTP request. For example, you want to POST something to https://example.com/data You send me these headers: POST /data Host: example.com Date: Sat, 24 Feb 2024 14:43:48 GMT Accept-Encoding: gzip Digest:…
Continue reading →

You type in to your browser's address bar example.com and it automatically redirects you to the https:// version. How does your browser know that it needed to request the more secure version of a website? The answer is... A big list. The HTTP Strict Transport Security (HSTS) list is a list of domain names which have told Google that they always want their website served over https. If the user …
Continue reading →

I've responsibly disclosed a small security issue with Mastodon (GHSA-8982-p7pm-7mqw). It allows a sufficiently determined attacker to use any Mastodon instance to redirect unwary users to a malicious site. What do you think happens if you visit: https://mastodon.social/@PasswordReset/111285045683598517/admin? If you aren't logged in to that instance, it will redirect you to a 3rd party site.…
Continue reading →