Look, I know your company wants metrics. I know your boss wants to see the exact percentages of people who click on links in your emails. Your sales team are desperate to track conversions. Someone wants to optimise your funnel for reasons which are unclear to you, a lowly engineer.
So you make the mistake of adding tracking to every email you send out. Including sensitive ones.
I recently signed up to online learning platform Udacity. As part of registration, they want me to confirm my email address. Pretty normal behaviour.

Because I'm a paranoid fellow, I wanted to see where the big VERIFY EMAIL link went.
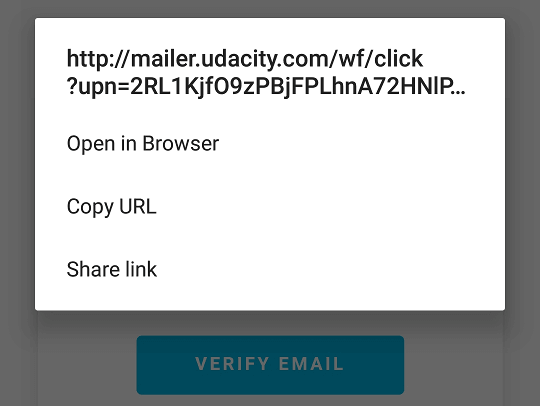
Ah! An insecure http link to their email tracking platform.
Never mind, thought I, there's a plain link underneath that one. Hmmm.... I wonder where that goes.
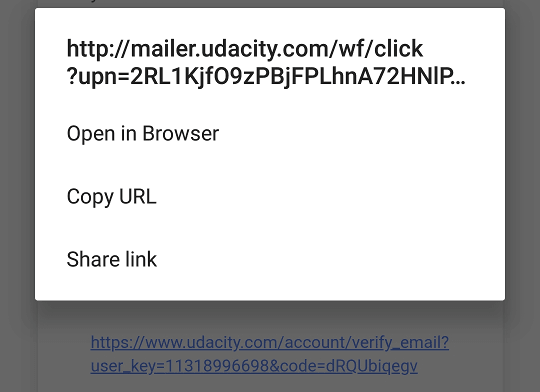
Oh, right. That's also insecurely tracked. To be clear, the text of the URl is https but the link it points to is http.
What's the problem?
Links to http sites are not secure. That means your visit to that URl can be seen by your ISP and anyone else between you and your destination. Your ISP can change the contents of that page and a malicious entity could - potentially - hijack your credentials.
In this case, all the links go via SendGrid. You have no protection if they get hacked, or decide to harvest your credentials.
How to solve it?
STOP TRACKING EVERY LINK IN YOUR EMAILS!
Or, if you really have to - make sure your tracking server supports https.
Disclosure timeline
There's no dedicated security contact for Udacity. I went through their regular contact page
- 2018-03-11 Asked to make responsible disclosure
- 2018-03-12 Udacity asked for more information. I sent details & screenshots.
- 2018-03-13 Report accepted and bug bounty issued.
- 2018-04-13 Publication.
Reward
Obviously, for a vulnerability of this magnitude, I was expecting a bug bounty of several million dollars. Nevertheless, I'm rather pleased with my free Udacity T-Shirt, sticker, pen, and notebook 😊

2 thoughts on “Udacity Bug Bounty - or, please stop tracking every link in your emails”
Andrew McGlashan
I absolutely detest tracking links and deliberately avoid clicking them and seeking out the "offers" directly in my browser, avoiding any campaign tracking. Also, links to third party domains that claim to be acting for the first party (usually for customer surveys); why not have a single and properly used domain name for all your /work/ for the domain / service in question???
Decades ago I purchased WinZip, fully paid for, today I still get spam emails from them even though I have long since discontinued use of WinZip completely and I recommend against people buying WinZip or any of the product offers from them. They use a different domain name for tracking of their emails, different enough that I didn't know if it was trust-able, so I emailed them... they did confirm the other domain name was theirs too... the only positive is that they do their own tracking (or appear to be), but their tracking links are also plain old http too.
Most tracking is done via third parties and the tracking links are an awful abuse of user privacy.
rjc
One more case against HTML in email.
What links here from around this blog?