tldr;
- URL
http://[IP]/adm/file.cgi?todo=inject_telnetd - Telnet username
root - Telnet password
Aq0+0009
History
Four years ago to the day, I wrote an exposé of the hideous security failings of Sercomm IP Cameras. The blog has since attracted 200 comments - as people try to unlock their cameras, and find out what flaws they have.
Despite my best efforts at contacting Sercomm - the OEM who manufactures the cameras - and the "security" resellers who irresponsibly sell them to unsuspecting customers, the flaws remain unpatched.
Factory Reset
Most of the Sercomm cameras have a custom firmware which locks them down. As documented in my previous blog post, resetting the cameras is depressingly easy.
- Stick paperclip in the reset hole for a few seconds.
- The default login name is
administrator - There is no password set!
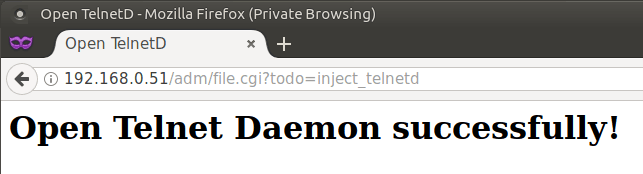
Turning on Telnet
The process for enabling Telnet was first published in 2011. It depends on the firmware that Sercomm have pre-loaded, but you just need to visit the specially crafted URl: http://[IP]/adm/file.cgi?todo=inject_telnetd
Firmware Trickery
Over on my GitHub repo of Sercomm API commands, you'll find a copy of the firmware for the iCamera 1000.
A contributor to the blog, Paul Chambers, describes how he deciphered the firmware.
The firmware is a modified SquashFS filesystem. Inside, it contains a symlink from
/etc/passwd -> /mnt/ramdisk/tmp/passwd
/etc/rc.sethostcontains the stringpasswdRunning rc.sethost does various things including writing a passwd file to
/mnt/ramdisk/tmp/passwdInside that, I saw
root:9sXicXdz8JrVk:0:0:root:/root:/bin/shThe string
9sXicXdz8JrVkis a traditional DES based hashI patched
rc.sethostto skip the call tocrypt. Then I got:
root:Aq0+0009:0:0:root:/root:/bin/shI double-checked it was correct by running
squashfs-root$python -c "import crypt;print crypt.crypt('Aq0+0009', '9s')"
9sXicXdz8JrVkSo the username is
rootand the password isAq0+0009
There you have it. Different cameras may have different firmwares with different passwords - but I'd guess that they all follow a similar pattern. This particular password works on Firmware version V3.0.01.29
Enjoy!
24 thoughts on “Telnet and Root on the Sercomm iCamera2”
Dennis A Vitali
Thanks , Was on the same hunt for my ebay NV412a, justb wanted to get Zoom function to work via FW upgrade from later Sercomm camera!!
ArcAiN6
I would be very interested in learning how he managed to unpack, modify, and repack the firmware. I’ve been wracking my brain trying to figure it out for the iCamera-1000 model, and unfortunately, the pre-loaded comcast firmware doesn’t dump the full FW image when you do a dump from the device. That means my only recourse is to find an original full sercomm firmware for it, or hack around with the partial images being shoved out by comcast.
Krytos
You can actually just tell the camera to install whatever firmware you want. Just use the API command below and substitute the firmware version you want to install.
/adm/auto_upgrade.cgi?new_fw_url=http://edge.xfinity-home.top.comcast.net/firmware/DYW9HZ-105-1002R08.bin
iCamera1000 Firmware Files (only ones I have found)
http://edge.xfinity-home.top.comcast.net/firmware/DYW9HZ-105-1002R08.bin
http://edge.xfinity-home.top.comcast.net/firmware/DYW9HZ-308-1002R17.bin
http://edge.xfinity-home.top.comcast.net/firmware/DYW9HZ-308-1002R19.bin
http://edge.xfinity-home.top.comcast.net/firmware/DYW9HZ-308-1002R22.bin
Marken
He probably dumped it with a ch341a reader. When you hack the camera you have root access and can change stuff but ever wonder why when it reboot those changes don’t stick? Don’t have access to write to the Rom, if you use the dump method you dump the entire fw can unpack it edit and modify whst you want repack it and install it or flash it back to the chip and wala. You now have modified fw that has your changes
Robert Monsen
I just tried your telnet enable + root username/password pair on my iCamera2 from xfinity, and was able to get in. Sigh. What a bunch of losers. It's January, 2019
akzorz
This root user name and password works, however you can generate your own and it works just fine.
Richard Amiss
Hello there! Thank you for the blog posts. I was wondering, in all your travels have you ever found any version of firmware for the iCamera2 ? I am able to get into the web interface on the modded ones either way, but I have 8 of them, some new with non modded firmware and some from old xfinity accounts and it would be so nice to get them all on the same firmware. Any leads, hints or links to the dark web are welcome!
Thanks!
Jaye diggs
This page has some info. Good luck!
http://itbyfire.blogspot.com/2017/03/hacking-xfinitys-home-security-cameras.html?m=1
prince noor
hi bro if you know about the upgrade version of rc4551 oc821 rc8221 so please let me inform i have 3000 thousand cameras in stock all have the F/W version problem please some body help me thanks to every one
Aseem Patnaik
Hello everyone I need some help. I have 2 of these cameras that i purchased thinking i could hook them up. I was able to connect both cameras to my router (hardwire and via wifi). However i do not see an IP address assigned to them to get in and get this thing figured out. From the little bit i know , without an IP i do not think i can do much. Are there any options for me or are these just paper weights?
Akzorz
You need to hold the button on the back for about 5 seconds then press wps on your router.
Akzorz
Just wanted to add that the CA cert installed on the camera is still good till next year! Common Name: XMPP Organization: iControl Organization Unit: OpenHome Locality: Redwood City State: CA Country: US Valid From: November 18, 2011 Valid To: November 15, 2021 Issuer: XMPP, iControl
Thanks for sharing
Mayank
Hi – I keep getting 404 whenever I try to save any config changes. This is same with API calls or GUI. I believe my camera is reset. Any insight will be greatly appreciated!
Rick McLeod
I have 3 iCamera2's from when I had an Xfinity security system. I have two of them working with the Windows IP Camera Viewer. But when I use the Android IP Cam Viewer Lite app, I can only view one of them. They both used to work. They both show up when I do an 'arp -a'. Not sure why the one works with the Windows app, but not the Android app.
The third camera doesn't show up at all when I 'arp -a', but it seems to go through the same sequence of led's ending with just one blinking on and off. I have pressed and held the reset button for more than 10 seconds, but no joy there. What can I try next?
Ian
I have a telstra branded icamera2. It was part of a now discontinued service from telstra.
If I try http:/[ip] I get Error 404. Is there a path I need to add ?
From looking through various other's responses I tried http://[ip]/img/media.sdp and it pops up asking for username and password, so something is alive in there. No suggested user/pwd combos work.
I've tried reset with power on and holding button for 10+secs but it reconnects to my wifi so I am imagining that I am failing the reset, perhaps that is disabled.
This camera is powered via the cat5 connector so I can't do a wired connection.
Any suggestions?
@edent
If it is powered over ethernet, you should be able to buy a PoE splitter which will let it connect to the ethernet port of your computer. That should stip it trying to connect to the wifi.
Jason anderson
So is there an app that I can connect this sercomm icamera2 to? I have access to the interface, figured that part out, but would really like to have an app to see. Any suggestions?
@edent
I use this app for Android - https://play.google.com/store/apps/details?id=com.alexvas.dvr.pro
Romans
Hi, is there any posibility to decode: admin_name=administrator admin_password=a679f2fec62be3f8f23cf731cfdbb596:
this is from config file
@edent
This is a very old post about extremely old cameras. You are unlikely to get a reply. It might help if you said the make, model, and firmware version of your device.
Romans
I dumped the FW of Sercomm (ADT) DBC835 Doorbell I think there only one FW exists, the internals are really interesting, it has even OpenVPN that's run on it and ton of apps. but they changed default administrator blank pass now it want's the password, shadow sends to null and didn't find any other place except config file that has it in AES.
sfm153
Wondering if there's an alternative to using just the ip address to access the admin window. I have two iCamera2 and can currently only access the GUI Admin Window with one (SCDADFB4 with access & SCF77D76 without access) . I had the other set up to connect to my router wirelessly and it appears to have downloaded a new firmware, since running the http://[ipaddress]/adm/get_group.cgi?group=SYSTEM shows defsys_ver=4.2 for the one wtih admin access while the other without access to the Admin Window shows defsys_ver=9.7 I've tried searching for API calls that might directly call the admin window like http://[ipaddress]/main.cgi?next_file=index_in.htm which is the page that the call to the ip address only brings one to. Alternately http://[ipaddress]/adm/system.htm is the main Administration menu.
sfm153
Wanted to add that despite getting the "404-Not Found" for the one wirelessly connected camera even after issuing the http://[ipaddress]/adm/enable_ui.cgi, and then just entering the IPaddress, both it and the other camera respond to many of the API commands such as: http://[ipaddress]/adm/get_group.cgi?group=SYSTEM and http://[ipaddress]/util/query.cgi I even had a batch file that would start the browser with the enable_ui command and then after a half second pause call a start for just the IPAddress for the camera which worked fine for the one wired camera but not the other.0
@edent
It is worth noting that this is an old blog post about ancient cameras. You may wish to upgrade to something more secure.