It is a truth universally acknowledged, that an ISP in possession of a good Internet connection must be in want of a customer.
One would think that, in these capitalist times, ISPs would compete over who could provide the fastest speed, the best service, and the lowest price. Sadly, in the UK, our ISPs seem to compete on who can be slightly less awful than each other.
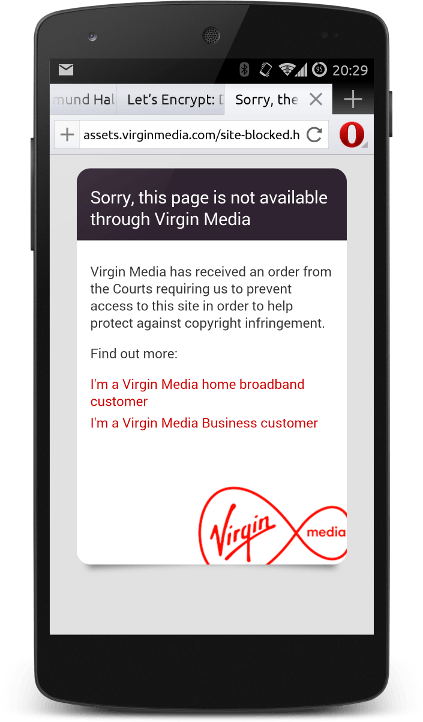
Last night, I did what many people normally do with their Internet connection. I made an HTTP request to open a website. Rather than receiving the site I had requested, I received this monstrosity from Virgin Media - my ISP.

I really was baffled. At first, I thought the site I was trying to reach had been blocked by the infallible British justice system. This is what Virgin customers see when they try to access a site blocked by the Great Firewall of Cameron:
I'd made several web requests during that session but, crucially, this was the first one that I had made over HTTP. The rest had all been secured via HTTPS. It wasn't even a salacious site I was visiting - unless cultural criticism of Barbie is too hot to handle nowadays.
Here's the thing though. I've a number of devices in my house, all of which make HTTP requests. My solar panels, my tablet, my TV, my radio, all chattering across the 'net on Port 80. Any one of them could have had their session hijacked. Perhaps they would have failed gracefully - perhaps not?
Perhaps some cheap piece of kit is sending usernames and passwords in plain text - now all that information has been redirected to my ISP.
I wasn't able to catch the exact exchange, nor the HTTP status code that redirected my session. All I do know is that my ISP broke the trust that it has with me. I pay Virgin to send and receive bits. Nothing more, nothing less. I don't want it interfering with my traffic outside the bounds of normal operations.
What next?
- Sorry to interrupt you ordering from Pizza Hut - we'd really like you to try a slice from Dominos?
- Sorry to interrupt you listening via Pandora - we've done a deal with Spotify, so try that instead!
- Sorry to interrupt you placing an order with a new ISP - please give us another chance!
Virgin send me an email with my bill. They also post me endless leaflets asking me to upgrade to their TV service. If they wanted to contact me about their new "Web Safe" system, they have ample opportunities to do so without monkeying around with the service that I'm actually paying for!
This sort of session hijacking is... I struggle to adequately describe it. Disgraceful is probably the word that comes closest. It is a Man In The Middle (MITM) attack. It impairs the operation of my computer. It's just rude!
And, the icing on the cake, Web Safe isn't very good.
There's a plaintive thread on Virgin Media's community forums asking for help with Web Safe:
is there a way to block only on-line betting/gambling sites i.e. make it impossible for anyone in the house to gamble away real money ?
I don't see any obvious solution on the f-secure or the web safe pages.
I don't want to filter my connection - but I appreciate that some people want to place limits in order to protect themselves. Web Safe can't do that. You can only opt out of sex, drugs, and rock'n'roll crime.

Why is Virgin Media doing this?
As part of our commitment to the UK government's initiative to improve child safety online, we're giving all our customers the chance to decide if they want to switch on Web Safe, our suite of parental controls.
From October until December, you will occasionally be redirected to a branded Virgin Media web page when you're browsing the web.
Please watch out for any other pages claiming to encourage you to switch on parental controls during this period, as these will not be from us, and may put your online security at risk.
Yup, Call-Me-Dave and Theresa May-Not have decided that we aren't sufficiently puritanical in our online browsing. Despite their hectoring and scaremongering, fewer than 15% of households have switched on the censorship software.
Even the language of it leaves me crawling with horror. "There are some things online that you might not want your family to see" is reminiscent of the Lady Chatterly trial's infamous "Is it a book that you would even wish your wife or your servants to read?"
Let me briefly enumerate some of the many ways that Web Safe is a bad idea.
- It only works on your domestic connection. If you - or your wife - wants to get around it, switch off WiFi and use mobile data instead.
- As mentioned above, it's now an extra vector for web criminals to phish for your details.
- The risk of false positives - Virgin Media has a page where you can tell them that they've over-zealously blocked an innocent page - such as a church.
- The risk of false negatives - if you believe that Virgin Media are doing their job, you may believe that you are surfing encased in a cyber-condom and are completely free from the risks of infection.
- It fundamentally alters the relationship between the subscriber and the ISP. It allows them to pro-actively censor material that you request.
- By demonstrating their ability to hijack your browsing sessions - because the Government asked them nicely - it shows that they take no interest in standing up for the rights of their customers.
- It equates the free expression of sexuality with violence, hate, and criminal activity. If your house contains a person who is confused about their sexuality - cutting off their chance to understand what's happening to them is barbaric.
- It's likely that these filters will also block sexual health charities. That's probably a bad thing, right?
Web Safe is a rotten product which is being foisted upon users in a manner which is unbecoming of a decent ISP.
If you want to stop the government pushing more censorship and control onto the Internet, please join the Open Rights Group.


6 thoughts on “Why Are @VirginMedia Hijacking My HTTP Connections?”
Andrew Coulton
Not sure if you know that also when they switched on this man-in-the-middle system on the weekend of 8th November their websafe servers couldn't cope (from the looks of it) preventing any customer who hadn't already explicitly opted out from accessing the internet at all for several hours that evening. All HTTP requests were failing with "websafe.virginmedia.com failed to respond" or in some cases certificate or SSL protocol errors from the websafe host.
Lee Maguire
Did you have the opportunity to check if it prevented non-browsers from making connections? I'd recently raised the issue with the ISPs at a recent meeting about whether non-browser devices would be blocked, and I don't recall what Virgin Media said, but I remember that BT, at least, stated that they explicitly checked for browsers (which I took to mean User-Agent strings).
Terence Eden
I didn't. I was able to pop open another tab & continue browsing, so I don't think it was a blocking action. Mind you, I'd love to know which HTTP Status Code they thought was appropriate to use!
Does this still happen is you change the DNS to another provider?
BT Broadband does this annoying thing where if you hit a 404, it provides you with a page hosted by BT to tell you. Which itself returns a 200 (success) status.
sigh.
Terence Eden
Virgin don't let you switch DNS providers at the router level. Individual devices can change their DHCP settings to get DNS from OpenDNS / 8.8.8.8 / etc - but there's no way to automatically do it for all devices.
Stephen Williams
My sessions have also helpfully been hijacked and interrupted by Virgin Media. What a disgusting invasion of my privacy. What does Virgin Media think they trying to achieve in deliberately annoying their customers?? Worse thing is, there was no "not now" option; the only options required me to log in to my Virgin Media online account.
The fact that this loos just like a malware redirect makes their efforts even more questionable. Are they conditioning their customers' behaviour to comply with future phishing scams that they may encounter?