Spotted in London, yesterday. A large, Microsoft Windows-powered advertising hoarding has been hijacked. It's not uncommon to see broken-down Windows displays - I run https://windowsisbroken.tumblr.com/ - which is dedicated to pointing and laughing at such mistakes. But this is the first time I've seen a display repurposed for profit! It appears to be running NiceHash Miner Legacy. A…
Continue reading →
An annoying privacy violation from leading email newsletter company MailChimp. Responsibly disclosed on 2017-12-04. When you click a link on a webpage or an email, your browser opens up that link and sends the newly visited webpage a Referer Header. (The misspelling is a historical artefact.) This says "Hello new site, I was referred here by this previous website." This has some privacy…
Continue reading →

Me being grumpy and stupid again. I have an IP Camera on my LAN, I want to connect to it via HTTPS. I can't. Why is that? Why do this? I have a username and password to access my IP camera. And my TV. And my lightbulbs. And all my networked gadgets. If I try to enter the passwords on a modern browser, I get this error message: It is now an accepted fact that data should be encrypted…
Continue reading →
I've blogged before about how backward the Co-op bank is - sadly, they've not improved in the last few years. I needed to close down my business bank account. I hopped on to online banking, provided all my details, went through 2FA with a physical token, remembered my mother's maiden name and began searching the site. There was no way to close the account. Oh well, I guess I'll give them a…
Continue reading →
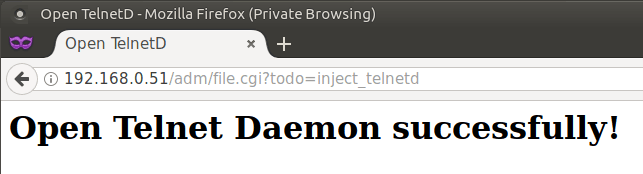
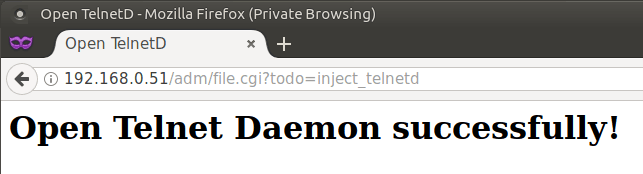
tldr; URL http://[IP]/adm/file.cgi?todo=inject_telnetd Telnet username root Telnet password Aq0+0009 History Four years ago to the day, I wrote an exposé of the hideous security failings of Sercomm IP Cameras. The blog has since attracted 200 comments - as people try to unlock their cameras, and find out what flaws they have. Despite my best efforts at contacting Sercomm - the OEM who …
Continue reading →

Just a quick note on a mistake I see people making. Webcam covers are a cheap and easy way to prevent your laptop's camera from spying on you. But too many of the covers obscure the LED which indicates that the camera is on. If you cover your activation LED then you won't be able to tell if a malicious entity has surreptitiously switched it on the camera. Keep it uncovered and you'll…
Continue reading →

Twenty One. I have 21 accounts which use Two-Factor Authentication. I use the Authy app to manage them all, but it is still a pain to scroll through and find the exact 2FA token I need. Encouraged by my friend Tom Morris's blog post, I picked up a YubiKey NEO for £50. It implements the FIDO U2F standard. Sadly, the YubiKey is substandard and frustrating to use. Here's what I found. First …
Continue reading →

Upon joining the hyper-local social network "Nextdoor" - users are asked to verify their postal address. One option they offer is to have them send you a card in the post. So, I signed up, entered my address, and waited. A few days later, this popped through my letterbox. A few random thoughts... ✅ This is a nifty way to lightly verify someone's address! A service could ask for scans of u…
Continue reading →

Companies face a complicated choice. Make things easy for the customers, or make things secure for them. Convenience seems to take priority most of the time. This forces companies to get their customers to risk their own security. In this example, we see Verizon Wireless asking their customers to type their passwords into Twitter for everyone to see! This is dangerous. It is likely that many …
Continue reading →

Phishing is the devious practice of tricking users into giving away their usernames and passwords to fraudulent sites. It is big business, and the best defence against it is constant vigilance. I'm going to walk you, step-by-step, through a scam that targetted me today. Along the way we'll see how to avoid falling prey to these monsters. It starts with a text I was sent this SMS from a…
Continue reading →

Amazon now let you secure your account with Two-Factor-Authentication (2FA). This means you can log on with a one-time password which changes every minute. For some reason, Amazon call it Two-Step-Verification (2SV) - but it is exactly the same as all the other 2FA solutions. The Process There's no direct link to 2FA settings. So the process is slightly convoluted. Assuming you are signed in …
Continue reading →

Gmail is usually pretty good at stopping spam from reaching my inbox. When it slips up, it reminds me of just how terrifying the modern internet is. Early one morning, I received this email from someone I know (details redacted by me). It came from his email, it has his signature at the bottom. This doesn't look like someone hijacking his email so far. I don't put much stock by "Protected…
Continue reading →