Code-sharing site GitHub automatically sends email notifications to users. If you've commented on an issue, you'll get an email each time there's an update. That's pretty handy. It also allows users to reply by email. The reply is then automatically posted in the issue thread. Also handy. But a little dangerous. Lots of people have email signatures which contain personal details. When these…
Continue reading →

There's a new bug bounty provider in town! The Belgian company Intigriti. This is a quick write-up of how I found a trivial bug in their own system. The EU has announced that it is providing funding for bug bounties on critical open source projects. They've split the programme between HackerOne and Intigriti. I signed up to Intigriti, and instantly received a confirmation email. Can you…
Continue reading →

Imagine the scenario. You're trying out some cool new Twitter app. It asks you to sign in via OAuth as per usual. You look through the permissions - phew - it doesn't want to access your Direct Messages. You authorise it - whereupon it promptly leaks to the world all your sexts, inappropriate jokes, and dank memes. Tragic! What's going on? Many years ago the official Twitter API keys were…
Continue reading →

A few months ago, British Airways' customers had their credit card details stolen. How was this possible? The best guess goes something like this: BA had 3rd party JS on its payment page <script src="https://example.com/whatever.js"></script> The 3rd party's site was hacked, and the JS was changed. BA's customers ran the script, which then harvested their credit card details as they were…
Continue reading →

Here's a curiosity which I found while stumbling through the Sony PlayStation store. The website loads internally hosted scripts using SRI (SubResource Integrity). Why? Does your work require you to swipe an ID card to access the building? That seems pretty normal. Does your work also remind you to keep your badge visible, and to challenge people who aren't wearing theirs? That also seems…
Continue reading →

Some external JavaScript libraries are dynamic. That's a problem for the SRI model of security. How can this be fixed? Definitions Suppose I want my website to have the latest version of the jQuery library. I might use a Content Delivery Network (CDN) to serve the code for me. <script src="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js"></script> If an attacker were to…
Continue reading →

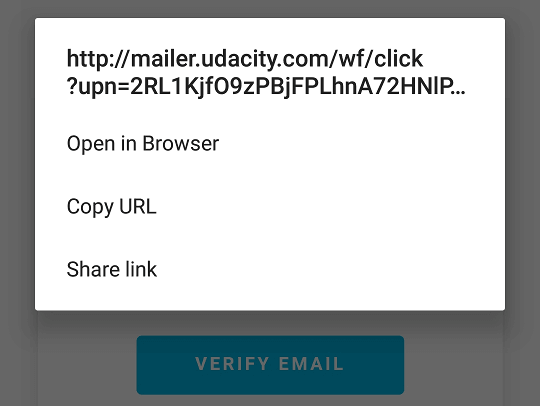
CloudFlare claim they want to secure the web - but they seem more interested in tracking their customers than giving them decent security. Upon registering with the Internet giant, users are encouraged to confirm their email addresses. So far, so standard. This is the confirmation message CloudFlare sends out: Looks good! Hey! I wonder where that garish orange button goes? WHAT!?! An http…
Continue reading →

One of the problems with the BlockChain goldrush is that it attracts a lot of people who don't necessarily have the required technical skill to safely run a service. This in turn reduces trust in the ecosystem. I'd like to discuss ArtChain.info - "Certifying Art Using the Bitcoin Blockchain" - and the some of the security issues I found there. XSS This is one of those simple bugs which every…
Continue reading →

A quick report into a nasty privacy vulnerability I found with the CAB. Unusually for me, this has no Internet component. Regular readers will know about my recent court visit. As part of that, I had to telephone the CAB Volunteers at the court who look after witnesses. I called, and was put on hold, then asked to leave a message. There's a popular myth that you can trick phone systems to…
Continue reading →

I'm going to tell you an anecdote which is a gross oversimplification of a complex topic. In the early half of the twentieth century, certain physicists made breakthroughs in relativity, quantum mechanics, and nuclear energy. Many of these scientists were Jewish. The Nazis called these heretical ideas "Jewish Science" and suppressed their teaching. Jewish physicists based in Germany fled the…
Continue reading →

Fake cash-machines are an increasing problem around the UK. Criminals attach all sorts of machinery - including fake fronts - to ATMs with the aim of stealing cash or card details. Wandering around Oxford yesterday, I noticed this sign attached to a bank's ATM: "This ATM is running slow and may take a while to return your card. Please be patient while we try to resolve this issue. Thanks.…
Continue reading →
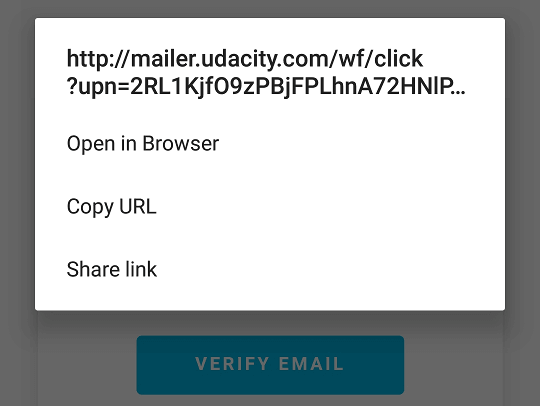
Look, I know your company wants metrics. I know your boss wants to see the exact percentages of people who click on links in your emails. Your sales team are desperate to track conversions. Someone wants to optimise your funnel for reasons which are unclear to you, a lowly engineer. So you make the mistake of adding tracking to every email you send out. Including sensitive ones. I recently…
Continue reading →