I found this on a security-related Slack (shared with permission). It launched an entertaining discussion about the risks of taking a potentially fake FIDO token. We all know the risks of taking a free USB drive and shoving it in our computer, right? USB sticks can install software, act as a keylogger, transmit data over WiFi, and even physically damage the electronics! So a USB Yubikey…
Continue reading →

I found this book while following a citation trail for my MSc. Published before the 21st Century (fuck, I'm old) it's a run-down of this new-fangled thing called Information Warfare. It covers electronic attacks, espionage, computer security and more. In the last 20 years, depressingly little has changed. If you removed the mentions of ActiveX and floppy disks, it'd still be 90% relevant. It…
Continue reading →

The FIDO specification defines a form of Universal 2nd Factor (U2F) when users log in to a system. Rather than relying on one-time codes sent via SMS, or displayed on a phone screen, these are physical hardware tokens which are used to supplement passwords. When used with websites, this technology is also known as WebAuthn. I use a USB thumb-drive sized hardware token and they're nifty - but a…
Continue reading →

I'm doing an apprenticeship MSc in Digital Technology. In the spirit of openness, I'm blogging my research and my assignments. This is my paper from the OPP module - where I can choose any subject. I picked Cybersecurity. You can read my Digital Leadership paper, my Data Analytics Paper, and my Business and Technology essay. I've previously written about the Art of Hacking course. The middle…
Continue reading →

Can you protect your home for £99? That's what this new X-Sense kit I've been sent claims to do. It's a LoRaWAN box with a claimed 2Km range for its variety of low-power sensors. The kit comes with two Infrared motion sensors, and four door / window sensors. Here's what it looks like: What's in the box? The base station is an anonymous white box, with a small speaker grille at the back and a …
Continue reading →

Julien Savoie has written a brilliant post explaining how you can enable https on your intranet. This is useful for several reasons. It means your employees aren't constantly fighting browser warnings when trying to submit stuff internally. All your http traffic is encrypted. You don't need to install a self-generated root certificate on devices. Lovely! But there's a downside. Every TLS…
Continue reading →

Chrome for Android had a flaw which let one tab draw over another - even if the tabs were on completely different domains. A determined attacker might have been able to abuse this to convince a user to download and installed a spoofed app. See Chrome Bug #1242315 for details. Demo Here's a video of me on one site (Twistory.ml) opening a link to Twitter in a new tab. Twitter's mobile site…
Continue reading →
As part of my MSc, I have to take an online exam. Obviously, this means I am highly likely to cheat by looking up things on Wikipedia or by having a bit of paper with notes on it. EVIL! So, the exam body requires me to install ProctorU. It's a service which lets someone watch you through your laptop camera while you do the exam. Creepy, but I get it. They also want to see your screen to make…
Continue reading →
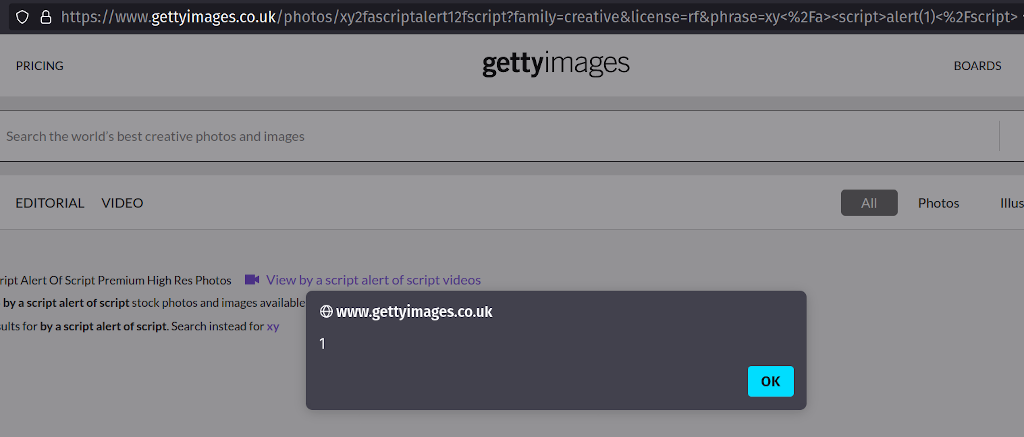
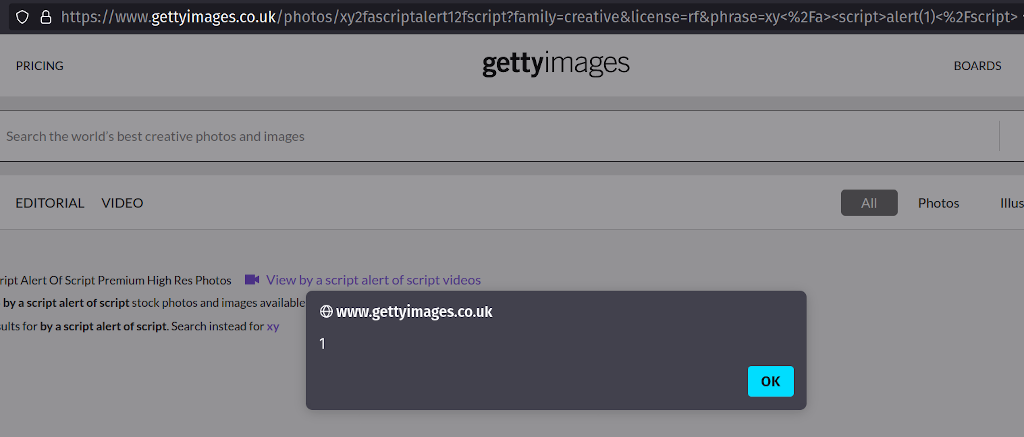
I've spent two months trying to report this issue to Getty images. They haven't responded to my emails, phone calls, Tweets, or LinkedIn messages. I've tried escalating through OpenBugBounty and HackerOne - but still no response. I've taken the decision to fully disclose this XSS because the Getty Images sites accept payments from users - and users need to be aware that the content they see on…
Continue reading →

In HTML, the autocomplete attribute is pretty handy. The HTML autocomplete attribute is available on <input> elements that take a text or numeric value as input, <textarea> elements, <select> elements, and <form> elements. autocomplete lets web developers specify what if any permission the user agent has to provide automated assistance in filling out form field values, as well as guidance to the …
Continue reading →

Legacy websites are a constant source of vulnerabilities. In a fit of excitement, a team commissions a service and then never bothers updating it. Quite often the original owners leave the business and there's no-one left who remembers that the service exists. So it sits there, vulnerable, for years. The [REDACTED] website had a subdomain which was running KANA's IQ software which was last…
Continue reading →

Bit of a boring write-up, but here we go. Taxi app Gett had a content injection flaw in its search function. By searching for an HTML string, it was possible for an attacker to add links or images to a page. It was really hard to contact them - but the threat of media attention sprung them into action. For example, searching for a specially crafted string meant that an arbitrary SVG could be…
Continue reading →