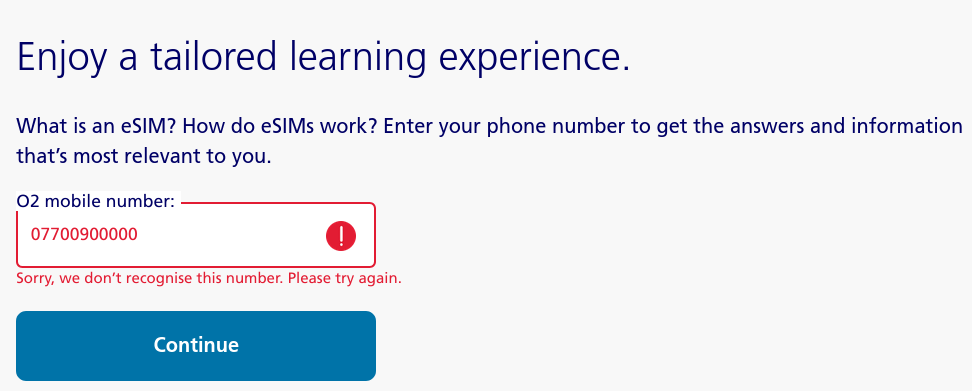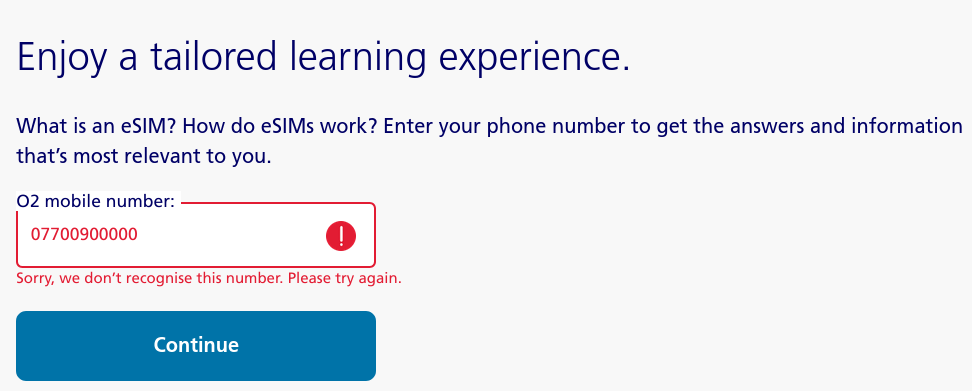
It's always fun keeping your network inspector tab open. While looking around the O2 UK website, I found this page all about eSIMs. For some reason, it wants to know the user's phone number. I put in a random number, and it refused to let me in. Putting in a genuine O2 number let me through. So what is it doing to validate numbers? It is making an API call to this URl: …
Continue reading →
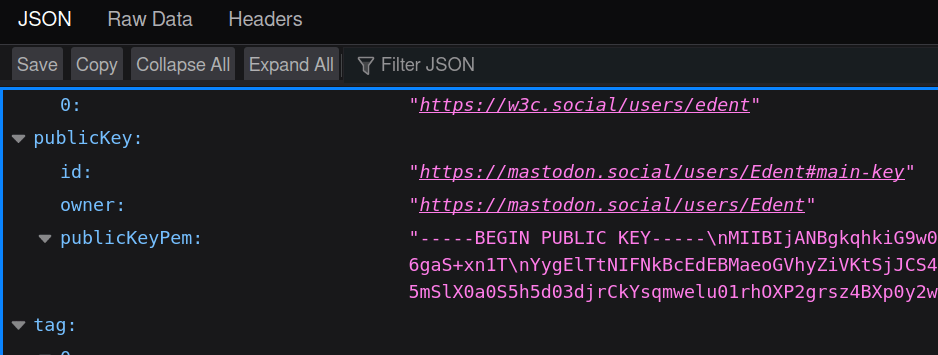
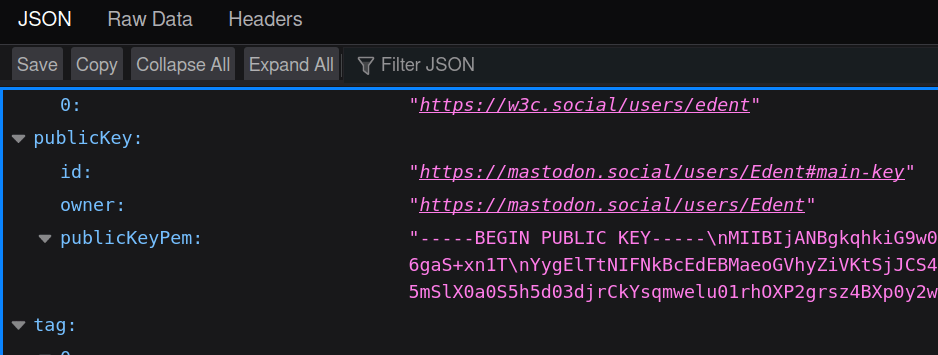
Mastodon makes heavy use of HTTP Message Signatures. They're a newish almost-standard which allows a server to verify that a request made to it came from the person who sent it. This is a quick example to show how to verify these signatures using PHP. I don't claim that it covers every use-case, and it is no-doubt missing some weird edge cases. But it successfully verifies messages sent by…
Continue reading →
Sometimes a client asks me a question and I'm a little stunned by their mental model of the world. A few weeks ago, we were discussing the need for better cybersecurity in their architecture. We spoke about several aspects of security, then they asked an outstanding question. "What should I buy to be secure?" It took a few moments to tease out exactly what they thought they were asking. In…
Continue reading →

You type in to your browser's address bar example.com and it automatically redirects you to the https:// version. How does your browser know that it needed to request the more secure version of a website? The answer is... A big list. The HTTP Strict Transport Security (HSTS) list is a list of domain names which have told Google that they always want their website served over https. If the user …
Continue reading →

I've responsibly disclosed a small security issue with Mastodon (GHSA-8982-p7pm-7mqw). It allows a sufficiently determined attacker to use any Mastodon instance to redirect unwary users to a malicious site. What do you think happens if you visit: https://mastodon.social/@PasswordReset/111285045683598517/admin? If you aren't logged in to that instance, it will redirect you to a 3rd party site.…
Continue reading →

Last night I received a call from my bank. They'd detected an unusual transaction and wanted to make sure that it was legitimate. Had I recently purchased £10,000 worth of crypto in the Maldives? What?!!? No! ARGH! I started to panic. All my apes money gone! No. Wait. The other thing. I knew it was a scam from the moment "James from your bank's fraud team" started his patter. You see, I have …
Continue reading →
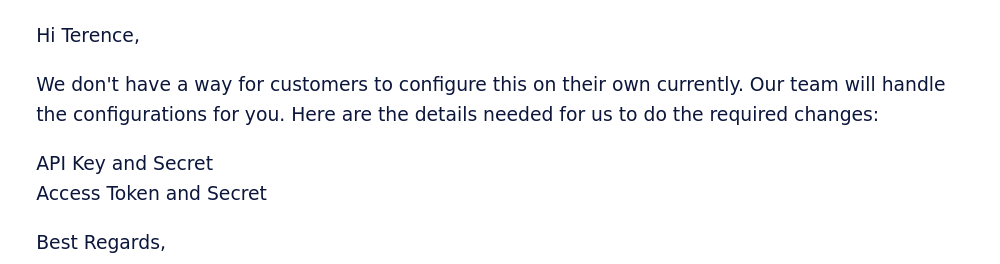
My CDN just asked me for all my Twitter API keys... WTF? This would give them complete access to my app's Twitter account, the ability to send and receive messages, and anything else that my API key allows. Giving them - or anyone - the entire set of credentials would be a very bad idea. What's going on? Twitter's slow-motion collapse and hostility to developers is causing a whole bunch of…
Continue reading →

Behold! Thanks to the power of the Watchy development platform, I now have all my 2FA codes available at the flick of my wrist! HOWTO This uses Luca Dentella's TOTP-Arduino library. You will need a pre-shared secret which is then converted into a Hex array. Use the OTP Tool for Arduino TOTP Library to get the Hex array, Base32 Encoded Key, and a QR Code to scan into your normal TOTP…
Continue reading →
I'm not thick. I know it doesn't sound like much of a boast, but I'm pretty competent at this whole adulting lark. But it appeared that I had forgotten a 4 digit number I'd set up less than a minute ago! The security guard smiled wearily at me, "It happens to everyone!" She said. Which, I'll admit was of small comfort. Work had taken the (sensible) decision that our entry cards weren't secure…
Continue reading →
Should my bank be able to block me from using their Android app, just because my phone is rooted? I'm reluctantly coming to the conclusion that... yeah, it's fair that they get to decide their own risk tolerance. Sage of the Internet, and general Sooth Sayer, Cory Doctorow once gave an impassioned speech on "The Coming War on General Computation". I'll let you read the whole thing but, I…
Continue reading →

This is a curious book. It starts out as a look at the security of everyday objects, but quickly becomes a series of after-dinner anecdotes about various security related issues. That's not a bad thing, as such, but a little different from what I was expecting. There's no doubt that Mikko walks the walk as well as talking the talk. Almost every page contains a bon mot. For example: Working in …
Continue reading →

Codeberg is a hip new code hosting site - similar to GitHub and GitLab. And, much like Gits Hub & Lab, users can serve static content through Codeberg pages. Somehow I screwed up my configuration, and when I visited edent.codeberg.page/abc123 I got this error: Now, whenever I see something from the request echoed into the page's source, my hacker-sense starts tingling. What happens if I…
Continue reading →