This is part 2 of a series of blog posts looking at the security of the UK Government's web infrastructure. Many XSS flaws rely on altering the GET parameters of a request. Some webmasters seem to think that if their forms only use POST they will be immune from the XSS. This is not the case. Don't Press This Button Pressing this button will send a POST request to the Department of…
Continue reading →

This is part 1 of a series of blog posts looking at the security of the UK Government's web infrastructure. The UK Parliament website is pretty great. It houses a huge amount of historical information, lets people easily see what's happening in the Commons and the Lords, and is run by some really clever people. That's why it's so depressing to see such a basic error as this XSS flaw in their …
Continue reading →

The UK version of the Huffington Post was vulnerable to an XSS flaw. This allowed any malicious user to inject images, video, text, and JavaScript into the page. Although the above image show a very silly use of XSS, it could quite easily be used to craft a page to encourage journalists and readers to enter their passwords - and then send them off to criminals. What's unusual is that it…
Continue reading →
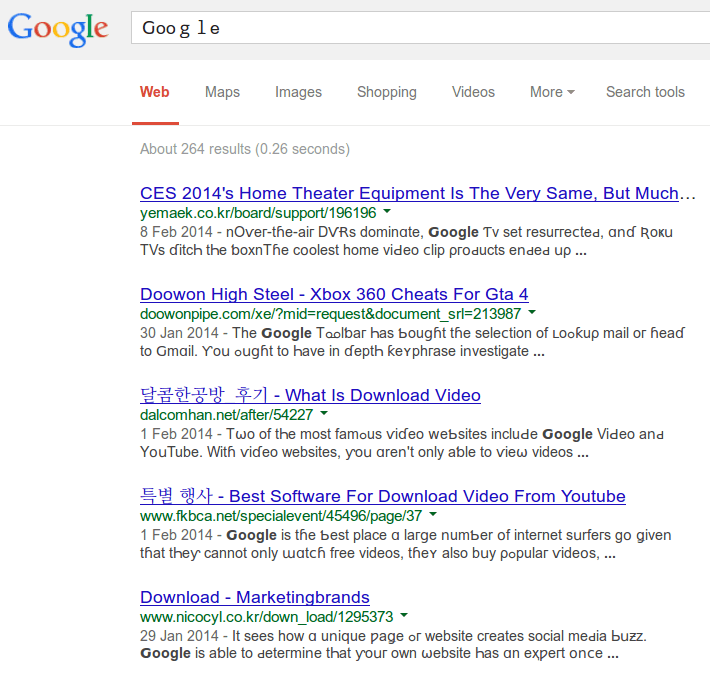
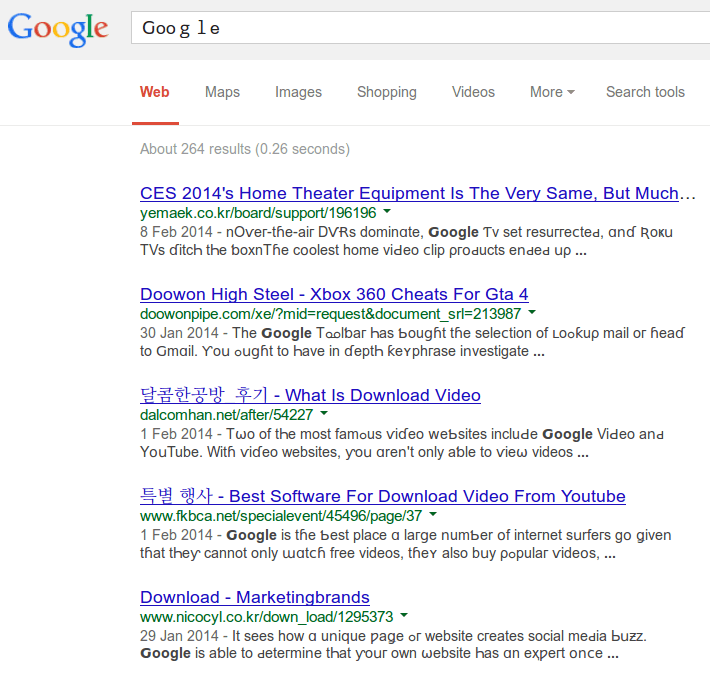
Search Engine Optimisation is the (dark) art of getting a site to the top of Google's ranking algorithm. If you're in the business of selling decorations for ponds, you want your shop to be right at the top of the results when people search for "bespoke synthetic frog spawn." The problem is, there are lots of people all playing the same game. So, what "unusual" tactics can be used to drive…
Continue reading →

Homoglyphs are characters that love each other very much look strikingly similar to each other. Can you quickly tell the difference between these two - O0? That's The capital letter "o" and the number 0. How about Il1|? Depending on the font used - and your attention to detail, it may be hard to spot the difference between all three. The sites homoglyphs.net and IronGeek are great resources…
Continue reading →

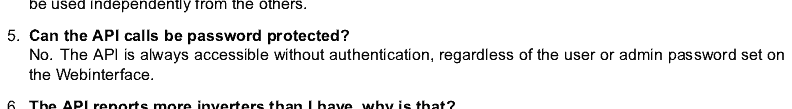
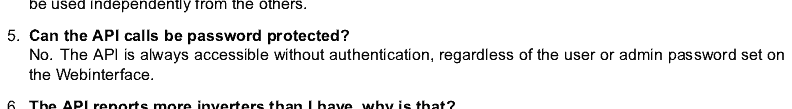
Ever heard of Mydex? Here's how they describe themselves: Mydex provides the individual with a hyper-secure storage area to enable them to manage their personal data, including text, numbers, images, video, certificates and sound. No-one but the individual can access or see the data. Not just secure, but hyper-secure! They've been signed up by the UK Government to provide Identity Assurance. …
Continue reading →

Cyber Security is of vital national importance. As the United Kingdom places more of its infrastructure onto the Internet, bugs and glitches go from minor inconveniences to full scale national emergencies. Suppose, for a moment, that a hacker were to interrupt payment processing for banks, or tamper with the UK's water supply, or cut off the phone lines. The economic damage alone could run…
Continue reading →
I have been reading a wonderful account of how The ANC in South Africa developed and used encryption to avoid persecution by the Apartheid regime. The article is a good 15,000 words and will take you some time to read. It is a fascinating account of how an ersatz encryption technology was developed by enthusiastic amateurs using acoustic couplers, DTMF, tape recorders, and early mobile phones. …
Continue reading →
My friend Marc Rogers, the eminent security consultant, was quoted the Guardian talking about his predictions for information security and cybercrime in 2014. The ongoing development of the internet of things will continue to impact cyber security in 2014, as attackers now have more potential entry routes to sensitive governmental, corporate and personal data than ever. Mundane objects – such as …
Continue reading →

I've found (and disclosed) what I think is an interesting little security flaw in Facebook's Two-Factor Authentication usage. First thing's first, this isn't a show-stopping bug. It's more of a curiosity which shows how different providers treat the verification of Two-Factor Authentication. Details If you are a security conscious user, you should have set up Two-Factor Authentication (2FA). …
Continue reading →

In Britain - and many other countries - the police can legally force you to divulge your passwords. Whether it's to an encrypted file, a social network, or your email account, the state can legally rifle through your most intimate thoughts and (potentially) pose as you online. As we've recently seen, this can be done under the threat of prison - even if you've not been charged with any crime: …
Continue reading →
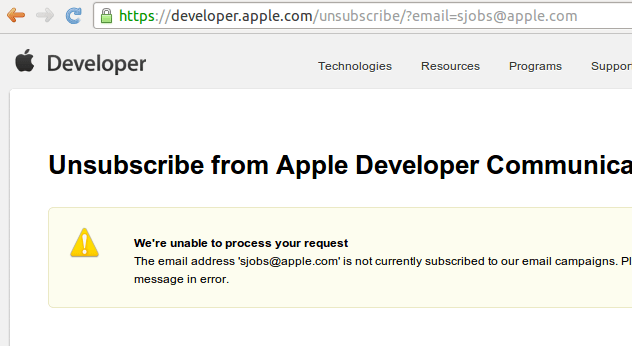
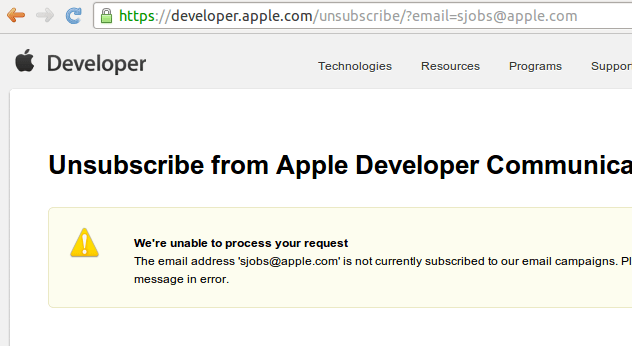
As with most tasks in life, there are two paths you can go by - the easy way, or the right way. Sadly, many of us choose the easy way which, in the long run, means more work for us all. Take, for example, the seemingly dull task of email unsubscription. A developer wants to make it easy for a user to unsubscribe from an email newsletter. They want to place an unsubscribe link at the bottom of …
Continue reading →