You cannot fail to have noticed that in most American films and TV shows, all the phone numbers start 555. This is a reserved number in the North American Numbering Plan. It means that it's a number which will never connect to a real person or service. So you can avoid the situation where a number is spoken on a show, or in a song, and everyone tries to call it - much to the annoyance of the…
Continue reading →

OAuth was designed to combat an anti-pattern. Typing your username and password into a third party site is bad idea. A really bad idea. I mean, you may think it's a bad idea to give your bank details to a Nigerian prince but that's just peanuts compared to giving away your password to an untrusted site! So, that's why we use OAuth. Rather than handing details to a random site, we authenticate…
Continue reading →

My good friend Richard Brent has often complained that my blog has very little Shakespeare content. Despite the domain name, I don't think I've ever blogged about The Big S. For shame! Fear not, my Brentish-Boy, this post is all about Shakespeare. And MySQL.... Ahem... When I first started shkspr.mobi it was intended to be an easy way to get Shakespeare on your phone. At that time, there…
Continue reading →

…
Continue reading →
We live in a world of our own creation. This means we can find it inconceivable that outsiders don't know the acronyms we use daily. How can anyone possibly live without understanding what we do? Customers don't understand your company's acronyms, processes, or business model. It's worse than that, though - most users don't even recognise your company's name! Here's a great example. In Zinio's …
Continue reading →

Here's a simple way to copy files to and from your BlackBerry PlayBook when you're using Ubuntu. This should work with any form of Linux. This is a step-by-step tutorial with screenshots. On The PlayBook Plug your PlayBook into your Linux computer using a USB cable. You may see this screen (or similar) you can dismiss it. In the Settings menu, scroll down to "Storage & Sharing". Ensure…
Continue reading →

In a mixed paradigm environment, how do you ensure content is surfaced which is context specific? By which I mean - how do you make your content serve the user's time-bound constraints? What I'm trying to say is - serendipitous discovery must be restricted based on temporal imperatives. Or, to break it down further, a user may only have a specific amount of time to dedicate to your app; how do …
Continue reading →

No. (N.B. I work for a mobile advertiser - but this is my personal blog. This post isn't written on their behalf. Naturally I'm biased.) (N.B. I'm in India and jetlagged to hell - this may not make any sense!) Wild headlines abound - but very few people seem to have read the original Microsoft sponsored paper. The 75% claim is based on... one app, running on the very first Android…
Continue reading →

I'm trying out the new Android app for Path - the new social networking service. I've discovered something rather troubling... Most of the app's communication with the Path servers is over SSL. This means that no-one can see the data you're sending and receiving. If there are snoops on your network, they will only be able to see the encrypted data flowing back and forth. In general, this is…
Continue reading →
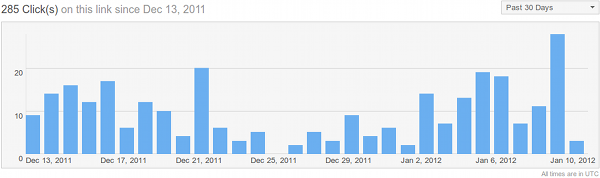
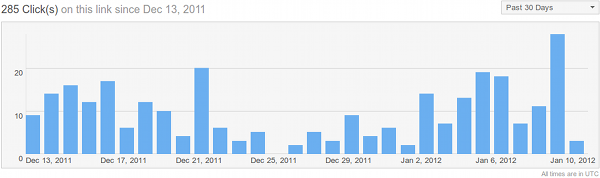
There was a lot of interest in my recent post about TfL's QR statistics. Today, I present to you three very different QR codes and their statistics. These are all taken from the Metro newspaper on Tuesday January 10th. Wowcher First up is "Wowcher", a big quarter page advert on page 28. Wowcher's statistics show a consistently good performance with QR codes. Between 30 - 80 scans per day,…
Continue reading →

You may have heard of "Range Anxiety". It's the worry that your car will run out of petrol before you have a chance to find a filling station. I have "power anxiety" - the crushing realisation that my smartphone's battery will be dead by lunchtime if I use it for more than five minutes. Over to Ben Smith: ... a frequent complaint is that we don’t want thinner phones. We’d rather manufacturers …
Continue reading →

(After Ben Metcalfe's post on the the vb.ly sage). As a mobile Internet consultant, companies often ask me which QR generator to use. There are many worth considering, but I always tell clients to avoid bit.ly. The security of Libya Internet organisations are probably not an immediate concern (you did know that's what .ly stands for, right?). What is worrying is how bit.ly exposes your QR…
Continue reading →