Quite often websites will encourage you to copy and paste commands into your terminal. There are a variety of reasons why this is bad - not least because someone could hide malicious code. That's usually done with a bit of CSS to make the evil command invisible, or using Javascript to inject something unwanted into your keyboard. Here's method that I hadn't seen before. Copy this code and paste …
Continue reading →

The other day, my HP M140w printer stopped working. The day before, it printed fine. This time, nothing. I rebooted, reset, updated, and performed all the modern rituals associated with uncooperative hardware. I logged into to the printer's webserver and clicked around the admin panel. On one page, I found an error message. So, like any self-respecting geek, I ignored what it said and Googled…
Continue reading →
Should my bank be able to block me from using their Android app, just because my phone is rooted? I'm reluctantly coming to the conclusion that... yeah, it's fair that they get to decide their own risk tolerance. Sage of the Internet, and general Sooth Sayer, Cory Doctorow once gave an impassioned speech on "The Coming War on General Computation". I'll let you read the whole thing but, I…
Continue reading →

I used to work in a call centre for a Very Big Company. Every week, without exception, we'd get a bunch of new starters to train. And every week, without exception, a newbie would be fired after looking up a famous person's data. This was in the days before GDPR. There was a lot less general awareness of data protection issues. It didn't matter how often will drilled it into trainees' heads -…
Continue reading →

Suppose you are sent a link to a website - e.g. https://example.com/page/1234 But, before you can access it, you need to log in. So the website redirects you to: https://example.com/login?on_success=/page/1234 If you get the password right, you go to the original page you requested. Nice! But what happens if someone manipulates that query string? Suppose an adversary sends you a link like…
Continue reading →

I needed a way to generate a TOTP secret using a fairly locked-down Mac. No Brew. No NPM. No Python. No Prolog, COBOL, or FORTRAN. No Internet connection. Just whatever software is native to MacOS. As I've mentioned before, the TOTP specification is a stagnant wasteland. But it does have this to say about the secret: The secret parameter is an arbitrary key value encoded in Base32 according to…
Continue reading →
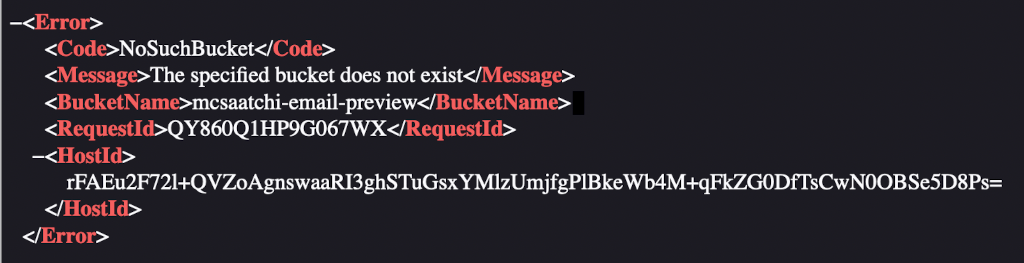
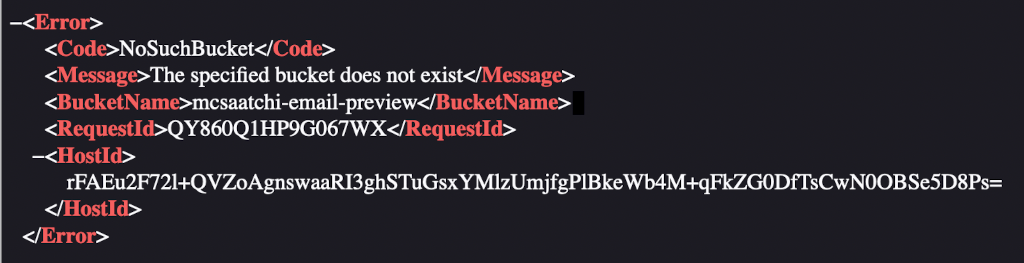
A few weeks ago, I received a billing email from my phone provider O2. While glancing at it, I noticed all the images were broken. Viewing the source of the email showed that they were all coming from http:// mcsaatchi-email-preview.s3.amazonaws.com/o2/... What happens if we visit that domain? Ah, the dreaded "The specified bucket does not exist" error. At some point the images were…
Continue reading →

This is a curious book. It starts out as a look at the security of everyday objects, but quickly becomes a series of after-dinner anecdotes about various security related issues. That's not a bad thing, as such, but a little different from what I was expecting. There's no doubt that Mikko walks the walk as well as talking the talk. Almost every page contains a bon mot. For example: Working in …
Continue reading →