A few months ago, I was attending the National Hack The Government event. I was showing off some of the work I had been doing on "The Unsecured State" - looking at *.gov.uk website security. I was chatting to an envoy from the Food Standards Agency who was eager to hear more about what I'd discovered. "Oh," I said, "It's pretty easy. Let's take a look at your website. If I were to type some…
Continue reading →

As part of my "National Hack The Government" win, I was awarded 100 DogeCoin! Although not my first foray into the exciting world of CryptoCurrencies, I'd never received DogeCoin before. I decided to set up an online wallet to temporarily store my loot while investigating more secure options. More or less at random, I went with DogeAPI.com. After registering, I received this email. Let's…
Continue reading →

While I was at the National Hack The Government hackday, I was interviewed by Chris Vallance - an amazing radio producer with the BBC. We spent quite a while talking about my findings of unsecured Government websites. It was a wide ranging chat, looking at spam, security, and the long term future of .gov.uk and .nhs.uk. He did a marvellous job of compressing it into a 5 minute piece which…
Continue reading →

It has been an intense few months digging through the security failings of the UK Government’s websites and trying to responsibly disclose them. It culminated with a week of blog posts exposing the vulnerabilities - and an award winning hackathon project. So what has been the reaction? The Good Privately, I've been contacted by people within the Civil Service who are working hard to make t…
Continue reading →
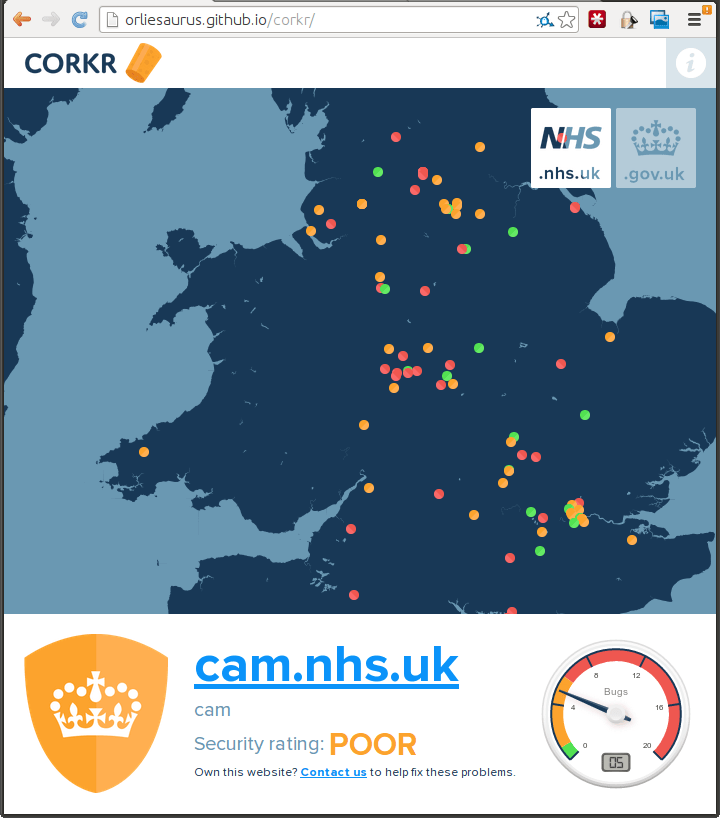
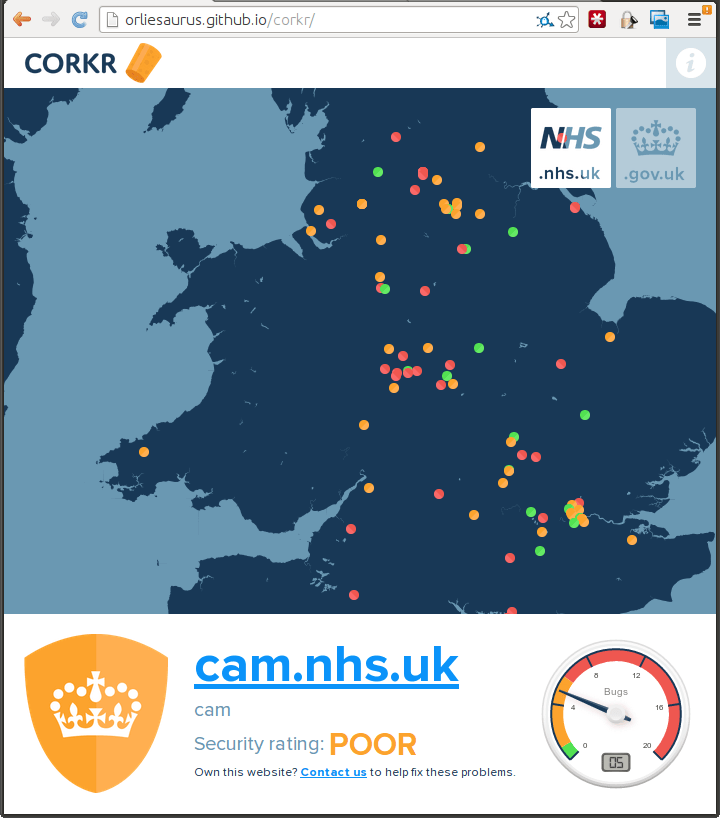
What a crazy weekend! I made the last minute decision to attend Rewired State's "National Hack The Government 2014" hackathon. Rather than hack on any of the provided datasets, I wanted to work on an interesting way to present all the security flaws I had found in Government websites. I teamed up with Mark, Marcello, and Orlando - together we created "Corkr - Plugging the Government's Digital …
Continue reading →

This is part 5 of a series of blog posts looking at the security of the UK Government's web infrastructure. The primary cause of the vulnerabilities I've exposed over this series is abandonment. In a flurry of excitement a website is commissioned and created. Then, as time wears on, people begin to drift away from the project. Job titles change, people are reshuffled, and senior…
Continue reading →

This is part 4 of a series of blog posts looking at the security of the UK Government's web infrastructure. Over the last few days, I've shown that hundreds of websites run by branches of the UK state are in a perilous state of disrepair. There are multiple sites with hugely embarrassing XSS flaws, running ancient and unsecured software, languishing unmaintained and long since abandoned. What …
Continue reading →

This is part 3 of a series of blog posts looking at the security of the UK Government's web infrastructure. Britain's National Health Service is riddled with old and insecure WordPress-based websites. Many of these sites have severe flaws including being vulnerable to XSS attacks. There is absolutely no suggestion that patient data or confidentiality has been put at risk. These flaws were …
Continue reading →

This is part 2 of a series of blog posts looking at the security of the UK Government's web infrastructure. Many XSS flaws rely on altering the GET parameters of a request. Some webmasters seem to think that if their forms only use POST they will be immune from the XSS. This is not the case. Don't Press This Button Pressing this button will send a POST request to the Department of…
Continue reading →

This is part 1 of a series of blog posts looking at the security of the UK Government's web infrastructure. The UK Parliament website is pretty great. It houses a huge amount of historical information, lets people easily see what's happening in the Commons and the Lords, and is run by some really clever people. That's why it's so depressing to see such a basic error as this XSS flaw in their …
Continue reading →

The UK version of the Huffington Post was vulnerable to an XSS flaw. This allowed any malicious user to inject images, video, text, and JavaScript into the page. Although the above image show a very silly use of XSS, it could quite easily be used to craft a page to encourage journalists and readers to enter their passwords - and then send them off to criminals. What's unusual is that it…
Continue reading →
There are some very sensitive souls on the Internet who object to seeing swear words. To that end, a huge industry has sprung up around "Profanity Filters" - services which claim to be able to detect naughty words and automatically redact them. The approach of dumbly looking for strings of text leads to a range of problems, including false positives (known colloquially as the Scunthorpe…
Continue reading →