Imagine the scenario. You're trying out some cool new Twitter app. It asks you to sign in via OAuth as per usual. You look through the permissions - phew - it doesn't want to access your Direct Messages.

You authorise it - whereupon it promptly leaks to the world all your sexts, inappropriate jokes, and dank memes. Tragic!
What's going on?
Many years ago the official Twitter API keys were leaked. This means that app authors who can't get their app approved by Twitter are still able to access the Twitter API.
For some reason, Twitter's OAuth screen says that these apps do not have access to Direct Messages. But they do!
In short, users could be tricked into allowing access to their DMs.
Restrictions
There are some restrictions which Twitter has put in place in the name of good security. The most important of these is restricting callback addresses. After successful login, the apps will only return to a predefined URL. That means you can't take the official Twitter keys and send the user to your app. This is a sensible security decision.
Except... Not every app has a URL. Or supports callbacks. Or is an actual app. Twitter has a secondary authorisation mechanism for such cases. You log in, it provides a PIN, you type the PIN into your app.
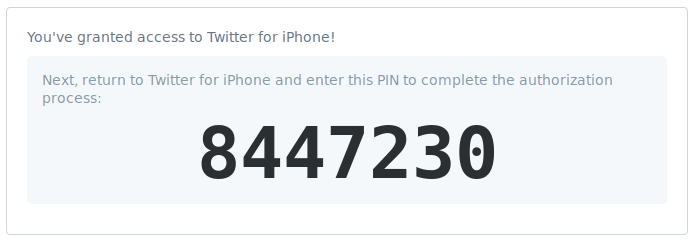
It appears that these official PIN apps don't display the correct OAuth information to the user.
Fixing it
Will Twitter audit old apps and make sure the permissions are correctly displayed? I hope so!
Ideally, Twitter should have a much more granular permissions model. Allow apps to read DMs, but not send them. Write tweets, but not delete them. Read Tweets, but not follow people.
Timeline
- 2018-11-06 Submitted via HackerOne
- 2018-11-06 Provided clarification and PoC. Issue accepted.
- 2018-11-15 Proposed publication date of 30th November rejected due to US holidays.
- 2018-11-16 Bug Bounty of $2,940 offered. Filled in the W2 form to say I'm not a US taxpayer.
- 2018-11-17 Drank a fair amount of cider.
- 2018-11-21 £2,287.05 deposited in my UK bank account. There was also the option of receiving it via PayPal.
- 2018-12-06 Twitter fixed the issue and published the bounty payout. They let me know I was clear to publish.
- 2018-12-07 I provided clarification that the issue was still present on some API keys.
- 2018-12-14 Published this report.
4 thoughts on “$3k Bug Bounty - Twitter's OAuth Mistakes”
Amal
Hi,
Is it possible to provide a poc video about how you verified the third party app accessed the messages?
@edent
You can read the Proof-of-Concept code at https://hackerone.com/reports/434763. I didn't make a video, sorry.
Trackbacks, Pingbacks, and Boosts
[…] *参考来源:shkspr、threatpost、hackerone,clouds编译,转载请注明来自FreeBuf.COM […]
[…] says that these apps do not have access to direct messages,” said Eden in a post about the flaw. “But they do! In short, users could be tricked into allowing access to their […]
What links here from around this blog?