Ever had a moan at your bank on Twitter? You're not alone - it's one of the most popular ways to interact with large companies. But how can you be sure that you're actually talking to the real customer services team?
There's been a worrying rise in the number of fake accounts which attempt to trick people into handing over their banking details. Let's take a look at one of them.
Here we see what looks like a genuine account from one of the UK's biggest banks - NatWest. This account belongs to a phisher - someone who wants to grab your banking details. In this example, the fake account is searching for people complaining to their bank - it replies and asks them to click onto a phony website.

Here, the user has been chatting with the real customer service team - as noted by the blue verified tick. The fake account continues the conversation!
 How sure are you that you wouldn't fall for this?
How sure are you that you wouldn't fall for this?
I was able to see most of the replies to this account before it was shut down. Some people were easily mislead.

That's worrying. But it gets worse.
Suppose you were fooled and clicked on the link. You'll be taken to a realistic looking website which asks for all your details.
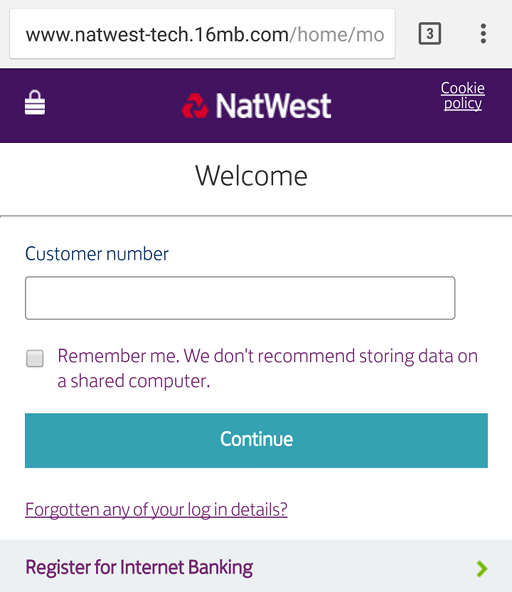
This looks identical to the real NatWest site. You've probably not noticed that this isn't the real NatWest domain, and that it isn't on HTTPS. Your mobile browser probably hasn't warned you that this is a scam - so you enter your real number.
That's where things get dark quickly.
Dark Phishing Patterns
Everyone knows that you shouldn't give away your full PIN. So the website only asks for the 1st, 2nd, and 4th digit. As soon as I hit submit, it gave me an error. Can you see what it has done?
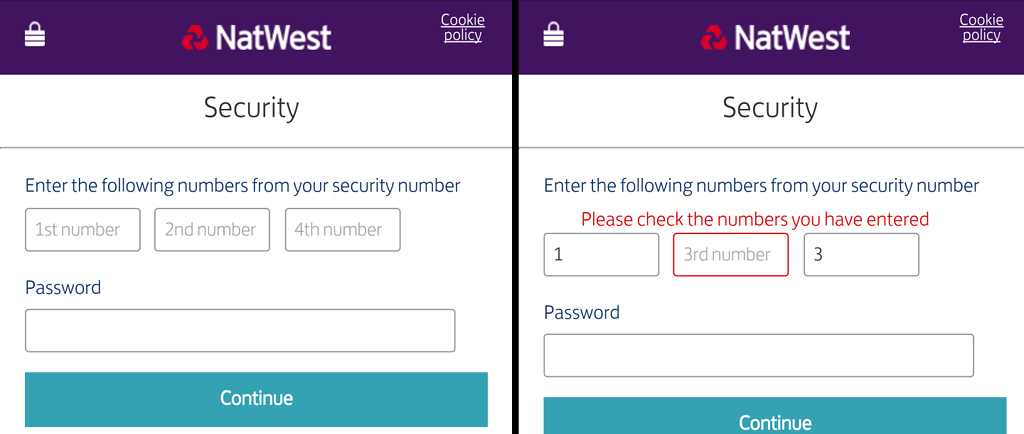
Now it is asking for the 1st, 3rd, and 4th digits! They now have your customer number, full PIN, and password.
Now they want more.
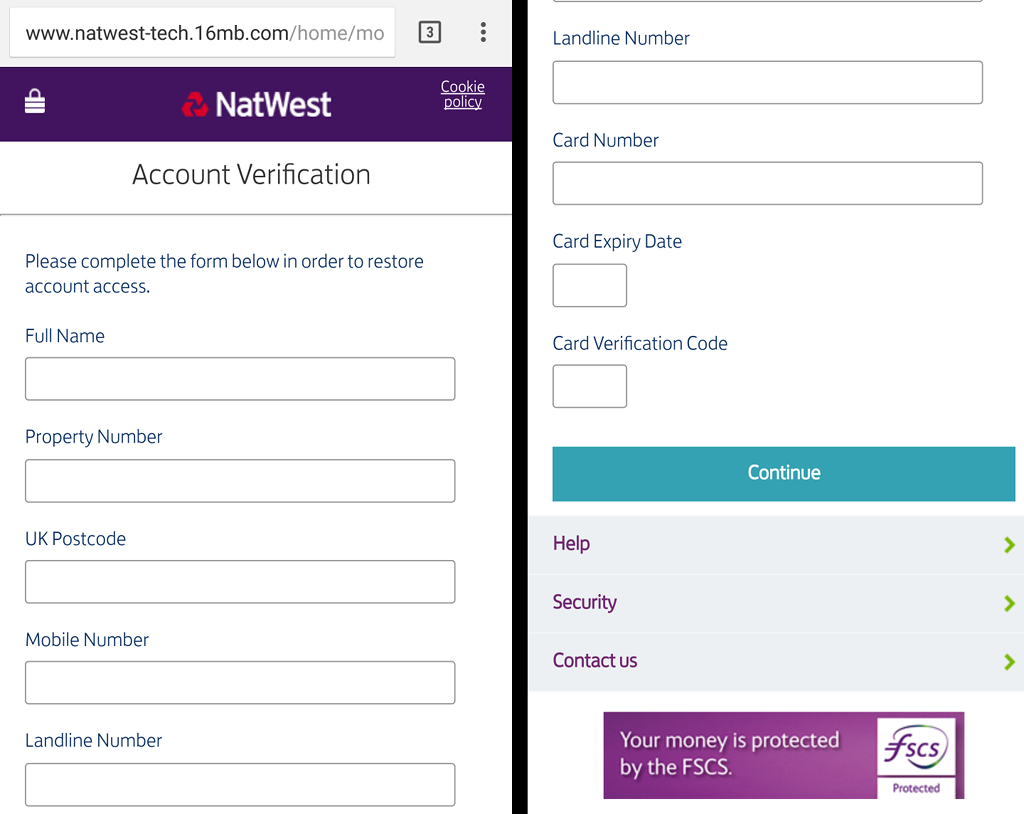
I'm just surprised that they didn't ask for my mother's maiden name and my first school!
With the above information, the criminals have everything they need to phone up your bank and impersonate you. Or to ring you up and impersonate your bank.
This sort of attack on customers isn't new - but as more people get online, there will be more criminals waiting to defraud the unwary.
4 thoughts on “Stop! You're talking to fake customer services on Twitter!”
Good article - I wrote a similar article yesterday for our company's website talking about a new email scam doing the rounds, and have updated it to include a link through to this post - http://www.source-design.co.uk/news/keep-alert-email-scammers-continue-to-get-more-convincing/
Doesn't seem like it would be disproportionate effort on the part of finance industry and browser developers to mitigate this. Institutions could forward their login pages to developers via an industry supported registry. Browsers could look at URLs, text, code and appearance (perceptual hashes, OCR), then issue a warning if the user navigates to a page that's suspiciously similar to a registered page.
You might be able to improve on that by having a standard HTML section for bank login pages which prohibits text chopping/combining, text as graphics/unicode homoglyphs etc.
Just an additional warning that a login page is being visited for the first time would help.
I suppose that scamers might stop using input elements altogether, making it harder to determine that a page is a login page.
Paul
The first giveaway is that the fake Twitter account doesn't have the checkmark. That's why the official accounts have it, to differenciate them from the fakes.
Yeah, the trick here is the real support replies first, then a phony picks up the conversation from there. Even if people know to check for that, they might not think to check every time.
What links here from around this blog?